Documents the process for creating users, managing user application roles, and managing user project roles.
The default security service implementation (SecurityServiceJpa) uses the IHTSDO user management system. Upon authentication, a REST call is made to the configured management service to validate the user and get some basic information. If authentication is successful, the map user information tracked by the application is updated to the latest state (including the user's name and email address). If there isn't a map user with that username yet in the system, one is added with a default VIEWER application role.
Thus, the sequence is something like this
The security service is configured by three properties in the config.properties file used by the running application.
ihtsdo.security.activated
ihtsdo.security.url=https://usermanagement.ihtsdotools.org/security-web/query/
The REST service URL to which an authentication call can be made
ihtsdo.security.timeout=7200000
If the "activated" flag is set to false, the behavior is a little different. In that case, the sequence is like this:
Thus, in an "inactivated" system, users cannot be created simply by logging in.
The default security service also has special handling for the user "guest" which is authenticated by any password. The default installation of the system runs the "import.sql" file which creates the "guest" user in the map_users table. That means this user always exists and doesn't require authentication. The sequence of events is exactly the same for guest login as for when security is inactivated (NOTE: this is true for guest user even if security is activated).
An admin user must exist in order to perform top-level application administration activities (such as changing the application role of a user to ADMINISTRATOR). In a new system without an existing user with role ADMINISTRATOR, there is a mojo for creating an initial admin user. See Creating an Administrative User for more details.
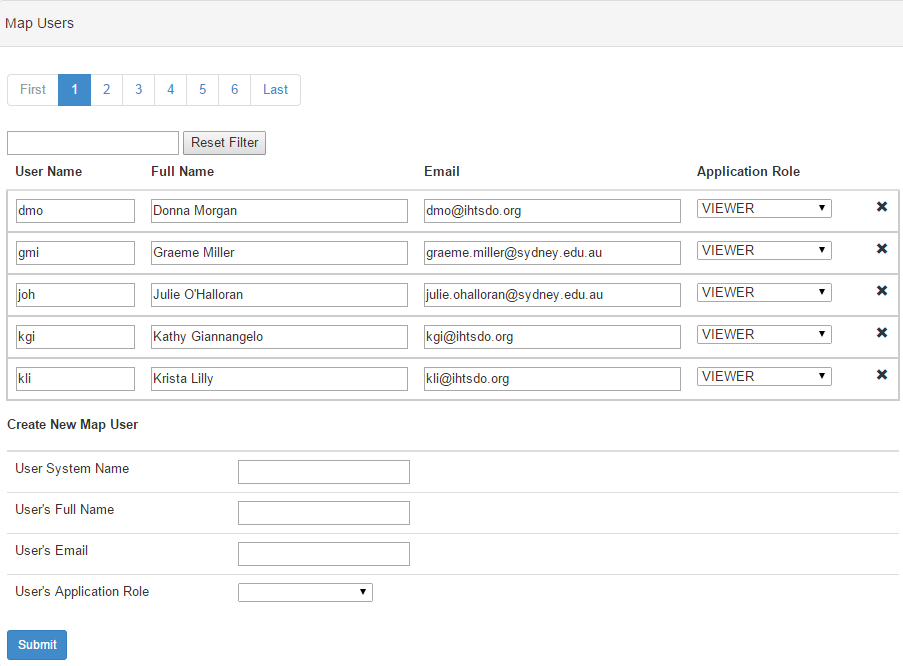
Once you have a user with role ADMINISTRATOR, you can log into the application with that role and use the "Map Users" accordion on the "Application Administration" widget (on the adminstrator dashboard). From here, you can create new users and edit the application role of existing users.
If no admin user exists, an admin user can be created using a mojo. To create the admin user, execute the following commands:
cd code/admin/loader mvn clean install -PCreateMapAdmin -Drun.config=YOUR_CONFIG_VARIABLE -Dmap.user=DESIRED_USER_NAME |
Executing this command will:
After execution, log in as the specified user to edit existing projects or the newly created Blank Project, create additional projects, or perform other administrative tasks.
It is strongly recommended that you create an ADMINISTRATOR user for administration and have separate users for lead and specialist roles on projects. Project roles override application roles when deciding which dashboard to show for a user. Thus, an ADMINISTRATOR user who is a lead on a certain project will see the lead dashboard instead of the admin dashboard when the focus project is set to that project.
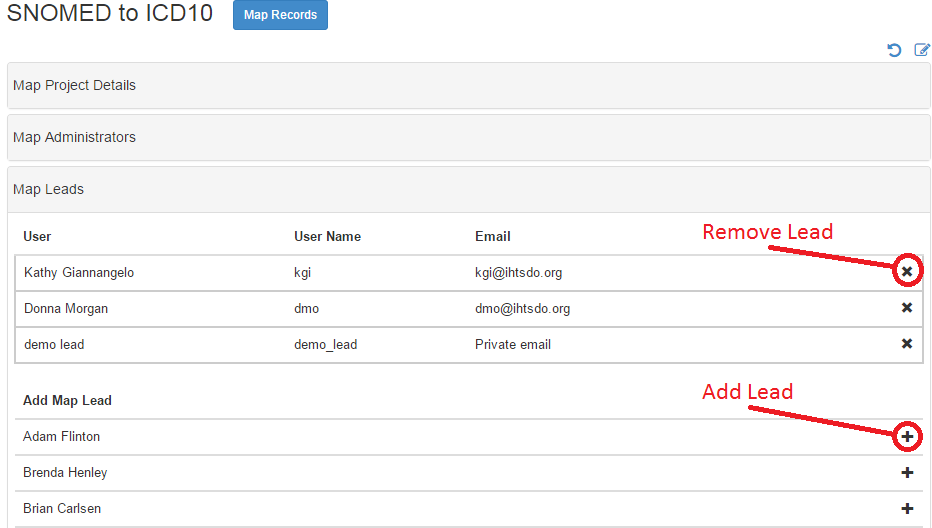
Project roles for existing map users can be set by lead or admin users via the "Project Details" page for a specified project.